My prod MoM (EM) server has come under a Nessus scan vulnerability that needs immediate remediation. I've opened up a case but not getting anywhere. So reaching out to the community. Surprisingly my DEV Env MoM (EM) is identical to Prod MoM yet that server didn't get hit with that vulnerability.
Since this is security hit for my org, it needs to be resolved ASAP or it could affect "athority to operate" for APM altogether.
Thanks in advance for any/all help with this issue.
Here are the details of the vulnerability:
35291 - SSL Certificate Signed Using Weak Hashing Algorithm
Synopsis
An SSL certificate in the certificate chain has been signed using a weak hash algorithm.
Description
The remote service uses an SSL certificate chain that has been signed using a cryptographically weak hashing algorithm (e.g. MD2, MD4, MD5, or SHA1). These signature algorithms are known to be vulnerable to collision attacks. An attacker can exploit this to generate another certificate with the same digital signature, allowing an attacker to masquerade as the affected service.
Note that this plugin reports all SSL certificate chains signed with SHA-1 that expire after January 1, 2017 as vulnerable. This is in accordance with Google's gradual sunsetting of the SHA-1 cryptographic hash algorithm.
Note that certificates in the chain that are contained in the Nessus CA database (known_CA.inc) have been ignored.
See Also
Solution
Contact the Certificate Authority to have the certificate reissued.
Risk Factor
Medium
CVSS Base Score
4.0 (CVSS2#AV:N/AC:H/Au:N/C:P/I:P/A:N)
CVSS Temporal Score
3.5 (CVSS2#E:ND/RL:OF/RC:C)
References
Plugin Information:
Publication date: 2009/01/05, Modification date: 2017/06/12
Ports
tcp/5443
The following certificates were part of the certificate chain sent by
the remote host, but contain hashes that are considered to be weak.
|-Subject : C=US/ST=New York/L=Islandia/O=CA technologies Inc/OU=CA APM/CN=ca.com
|-Signature Algorithm : MD5 With RSA Encryption
|-Valid From : Nov 26 06:16:57 2013 GMT
|-Valid To : Jul 16 06:16:57 2035 GMT
---------------------------------------------------------------------------------------------------------------------------------------------------
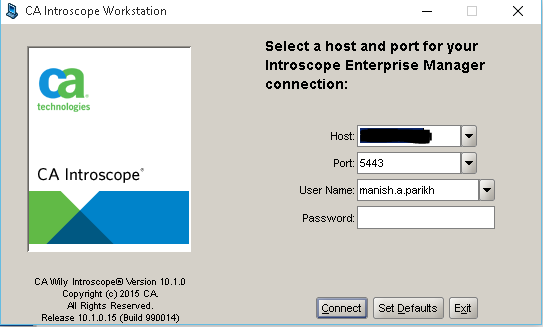
In prod environment, I use APM Workstation which uses port 5443 to access the UI. I do the exact same for the Dev env but doesn't seem to flag that at all